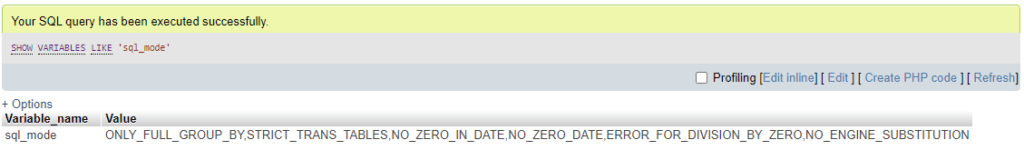
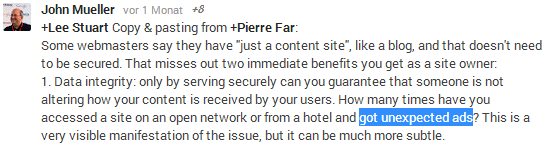
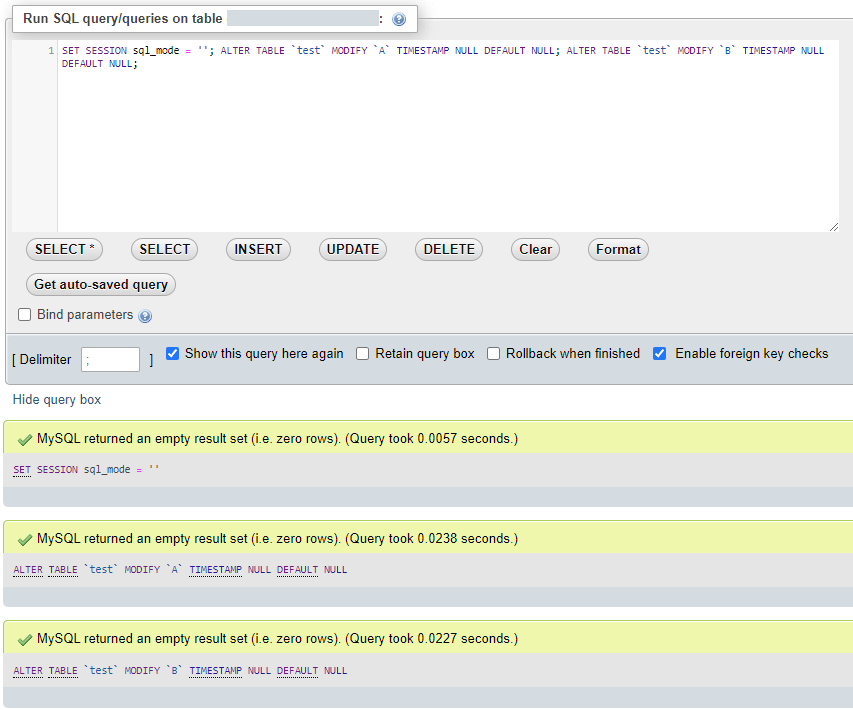
Pre-pending the query with SET SESSION sql_mode = ”; worked for me:
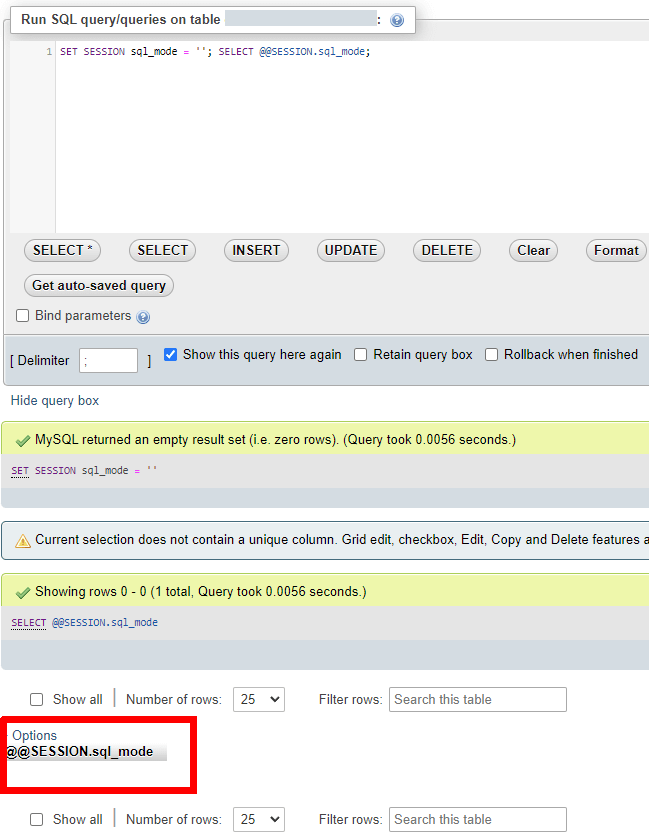
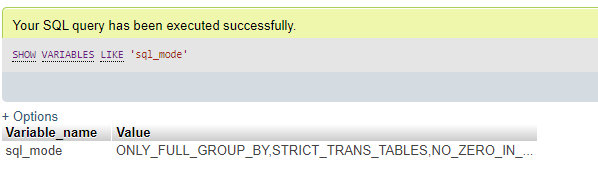
Note that executing multiple queries separately did not work. Here I ran SET SESSION sql_mode =” first and then SELECT @@SESSION.sql_mode, which showed that strict mode was still active:
Example
After the update of a MySQL server on a shared hosting account, strict mode was enabled with the NO_ZERO_DATE option and there was no way to change this. This meant that – among other things – I had to remove a default timestamp value of “0000-00-00 00:00:00” from multiple columns:
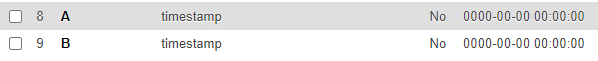
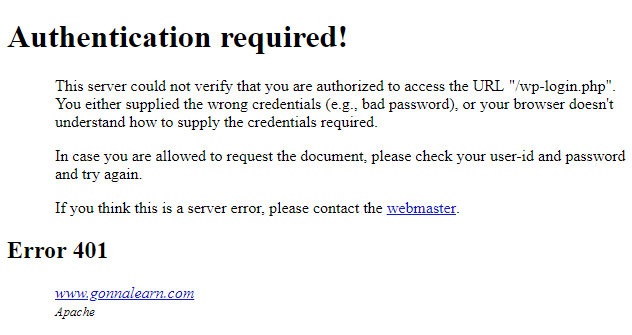
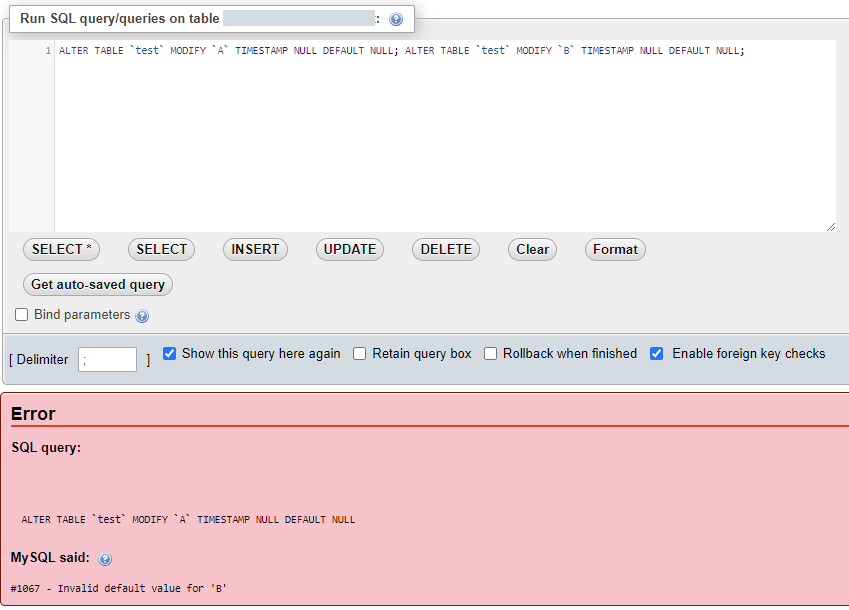
However this failed with error #1067 as other columns still used this invalid default. In other words, altering column A to make it compliant failed as column B was not compliant yet:
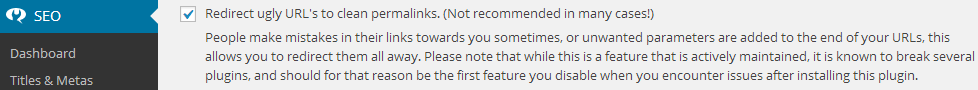
I’m not sure what the reasoning behind this is. However, temporarily disabling strict mode by pre-pending the query with
SET SESSION sql_mode = '';let me make the necessary changes:
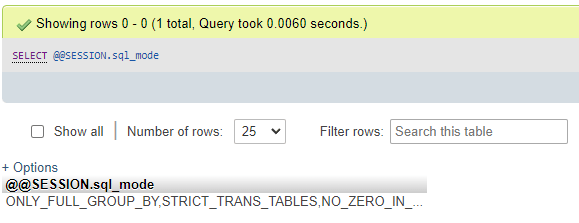
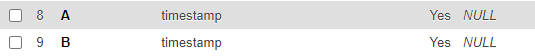
Result:
While this probably comes too late to help Pete, I hope it can help you.