Some restaurant websites in Luxembourg are poorly designed and make it difficult to find important information (such as the opening hours, the address or perhaps a menu that has been updated in this decade). What happened yesterday was even more confusing: I was immediately redirected to a suspicious page that claimed to conduct a survey.
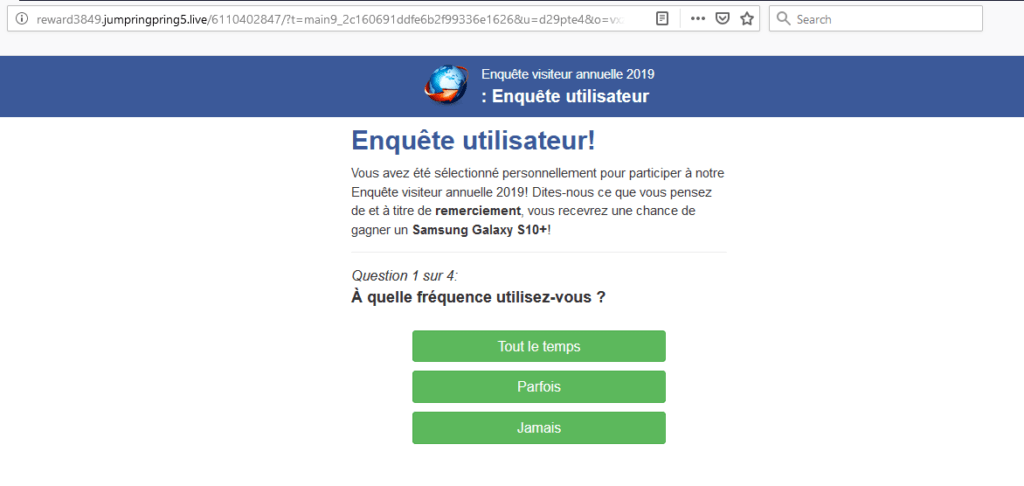
This is a so-called malicious redirect. The goal is usually to generate ad revenue for the hacker or to try to install malware on the vistor’s computer. I took this opportunity to test several tools which claim to be able to scan websites for vulnerabilities and malware. You’ll find the results below. Of course, I also notified the restaurant.
Notes:
- I didn’t hack the website.
- It’s not my website, which means I couldn’t test any popular tools which have to execute code on the server (e.g. MalCare, WordFence, WP Cerber Security). These tools may be more powerful although a malicious redirect should also be detected by external scans.
- This is obviously not a comprehensive test. I’m also not a security expert.
Google Safe Browsing
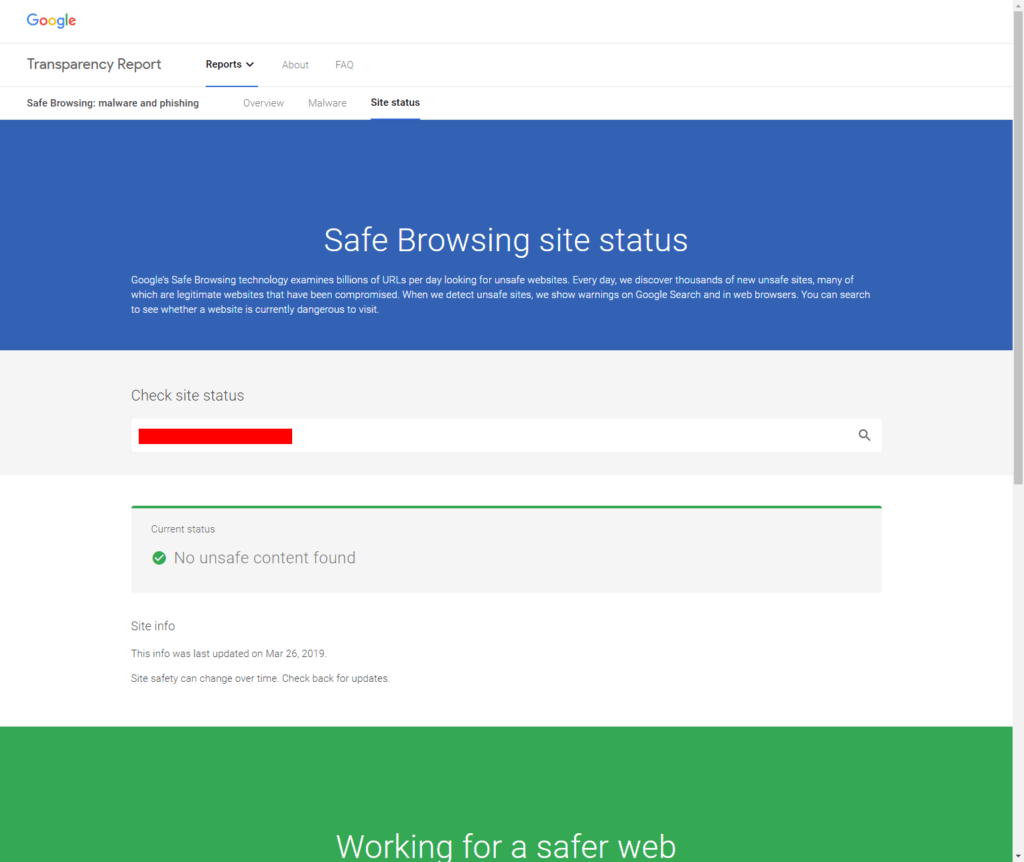
There’s nothing wrong with the website according to Google. However, the report was last updated on March 29, 2019 and it’s likely the website was fine then.
Hackercombat
Hackercombat asks for a name, business email and phone number before sending you the result of the security scan. The email I received confirmed that the “website has been affected by malware” and offered a link to a page with general information and a “100% free” malware cleanup service.
Quttera
Quttera‘s results were inconsistent. The website was first rated as clean. Shortly afterwards, it was classified as suspicious in a second scan:

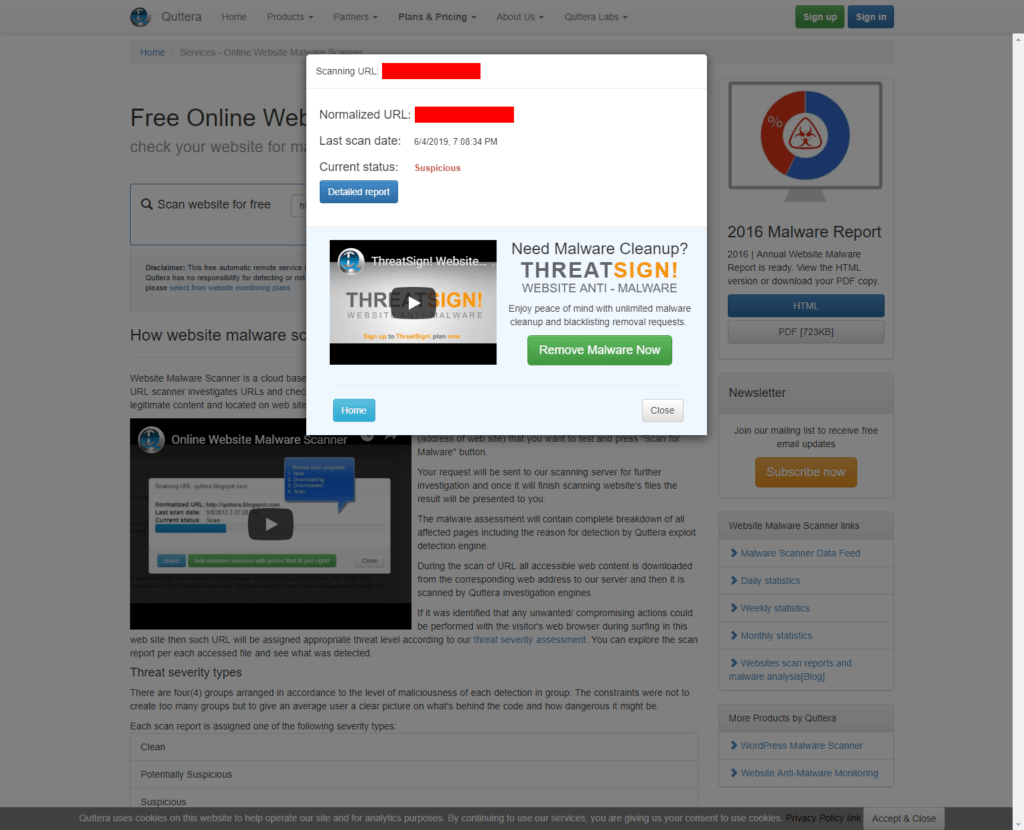
The detailed report did not clearly identify the issue as a malicious redirect.
ReScan.pro
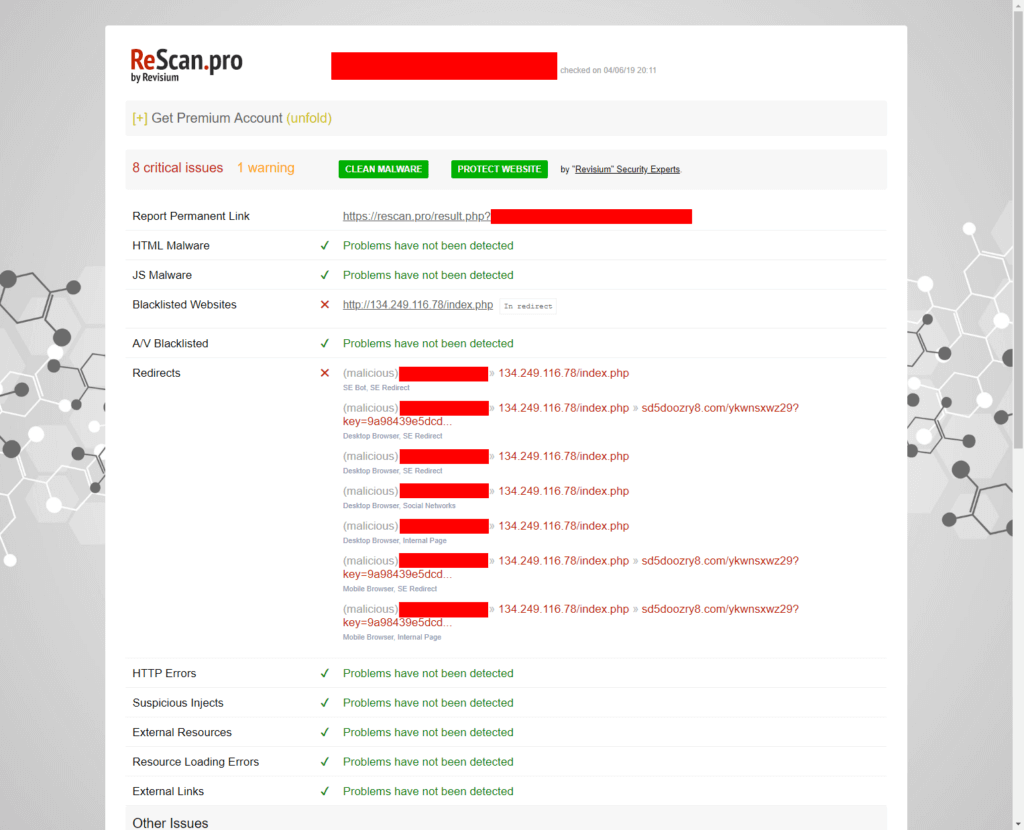
ReScan.pro consistently identified the malicious redirect and made it very clear that the website has critical issues.
SiteGuarding
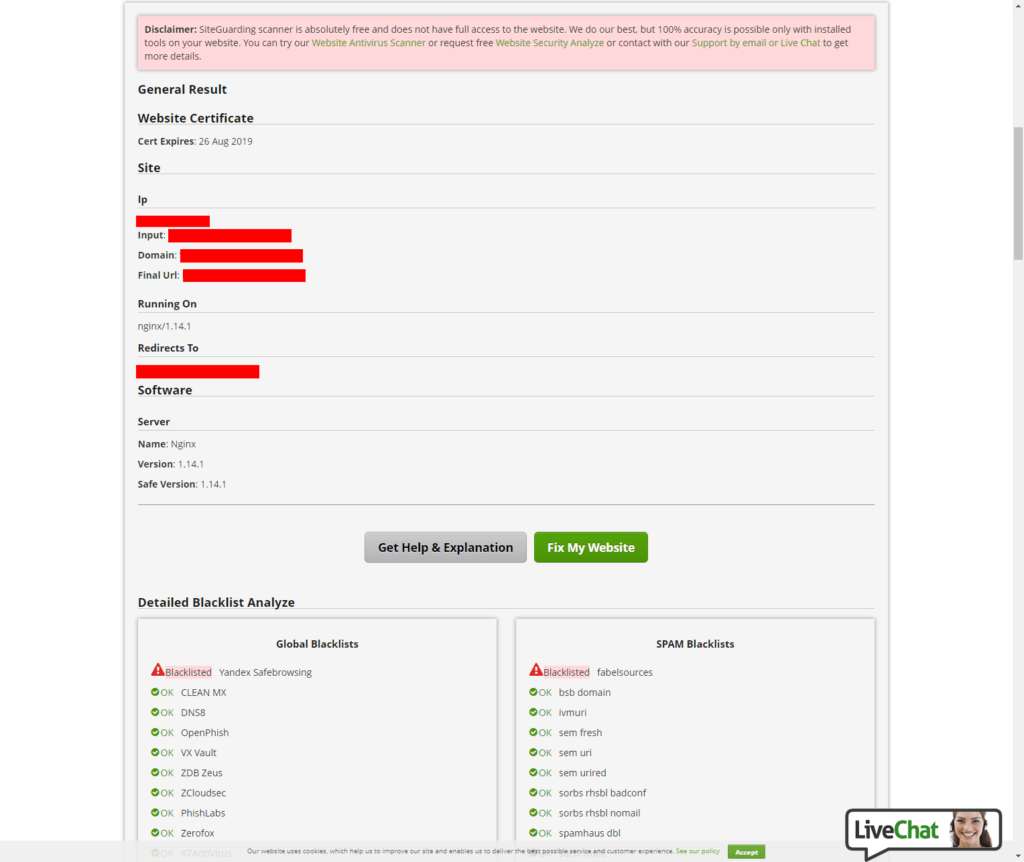
All that SiteGuarding’s malware scanner tells us is that the website was already blacklisted by Yandex Safebrowsing. Note: This scan and the second Sucuri scan were executed several hours after the other scans.
Sucuri
At first, Sucuri‘s external scan failed to detect the malicious redirect and claimed that no malware was found. It did complain about HTTPS mixed content which may have been a consequence of the redirect:

When re-testing the website several hours later, the report looked quite different:
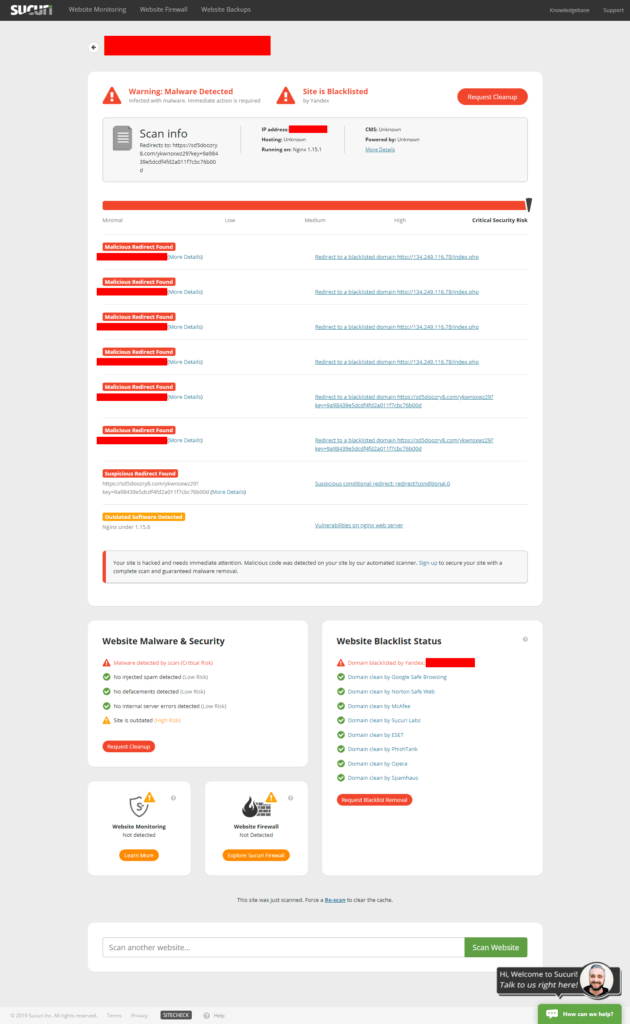
To make matters more confusing, it seems that the restaurant’s webmaster was already working on fixing the issue at this time (you can see in the second report that the CMS was now listed as “unknown”).
Web Inspector
I gave up on Web Inspector as it was still “waiting [for] a free detection server” more than 8 hours after I first submitted the URL.
Conclusion
The results are not entirely satisfying. While I didn’t expect an external scan to be able to tell me how the malicious redirect was implemented, it seems that most of the tools had difficulties detecting the redirect at all. Only ReScan.pro managed to quickly and consistently identify the issue while also giving me immediate access to the report.
To put it in another way, when I notified the restaurant, the only report I could include to show that this was indeed a problem on their side was the one provided by ReScan.pro. Quttera and Sucuri did not show (clear) warnings at the time, Hackercombat did not give me immediate access to their report and Web Inspector was useless.